Contents
With VMware removing the need for Windows Server for most of their solutions including vCenter, SRM, VROPS etc, I found that I only have 1 Windows Server remaining.
With its main purpose for simply hosing the DNS Server role, I decided to migrate my DNS server to PhotonOS, an ultra-lightweight Linux appliance with no license fees.
PhotonOS Setup
PhotonOS can be deployed in various ways and there is good documentation online for that so I won’t get into that here. For those who are interested, I simply downloaded the latest OVA from https://github.com/vmware/photon/wiki/Downloading-Photon-OS
Once PhotonOS is deployed into your vCenter Server or another environment, SSH to the appliance and log in with root / changeme.
After you have been promoted to change the password, follow these steps to install unbound, a free and open-source DNS server that works with PhotonOS without the need to compile something like BIND from scratch.
Static IP
As you’ll be using PhotonOS as a DNS server, you will likely want to assign a static IP.
Instructions for this are here: https://vmware.github.io/photon/assets/files/html/3.0/photon_admin/setting-a-static-ip-address.html
Installing & Configuring unbound
Update the system:
tdnf update
Install the unbound DNS server:
tdnf install unbound
Use VI to edit the unbound.conf file:
vi /etc/unbound/unbound.conf
As this was just for my lab, I wasn’t too concerned about performance or security so I simply applied the following configuration. If this is for production use, there are guidelines online on how to correctly secure the DNS configuration.
This is my basic configuration (I will step through it below)
server:
interface: 0.0.0.0
port: 53
do-ip4: yes
do-udp: yes
access-control: 192.168.100.0/24 allow
verbosity: 1
local-zone: "lab.local." static
local-data: "vcsa-01.lab.local A 1.2.3.4"
local-data-ptr: "1.2.3.4 vcsa-01.lab.local"
forward-zone:
name: "."
forward-addr: 8.8.4.4
forward-addr: 8.8.8.8
- The server section is simply the core server settings for the DNS server
- Leaving the interface as 0.0.0.0 will force the server to listen on all IP addresses
- port, do-ip4 and do-udp are straightforward
- access-control is used to limit which IP addresses can query the DNS server, you will need to change this for your environment.
- Next up are the zones
- So I have a zone for lab.local, and I have 1 A record for vcsa.lab.local with an IP address of 1.2.3.4
- You can add more A records by copying this line and amending as required
- I also have a PTR record for the corresponding A record listed
- The forward zones are there to configure where queries go to that are not in a locally defined zone. I have specified the public DNS servers from Google here
Creating the Firewall rule
Once you have saved this file, we need to add a firewall to enable UDP port 53 inbound on interface eth0:
iptables -A INPUT -i eth0 -p udp --dport 53 -j ACCEPT iptables-save >/etc/systemd/scripts/ip4save iptables -L
Setting unbound to start on boot
Finally, we need to make unbound start at boot time and start it now for testing:
systemctl enable unbound systemctl start unbound
Testing
Now all we need to do is set another system to use this new PhotonOS machine’s IP address as it’s DNS server.
Once you have done that, all you need to do is edit the configuration file above to add A and PTR records for each additional server you need to resolve IP addresses for in DNS.
To test a simple ping or NS lookup of something in the local zone and remote zone should suffice.
Troubleshooting
If the DNS server stops working for some reason, follow the below to find out why:
Stop the service:
systemctl stop unbound
Try to start the service again:
systemctl start unbound
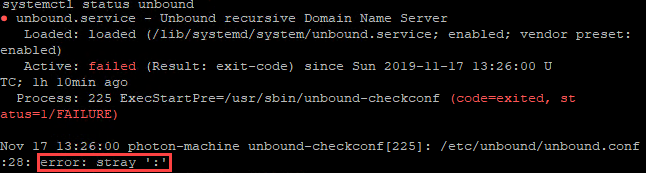
Now run status to see if there were any errors when starting:
systemctl status unbound
Sometimes you might make a mistake in the configuration file. Fortunately, running systemctl status unbound will parse the config and alert to any syntax errors that you might have:
Next Post: Setting up an NTP server on PhotonOS








[…] previously wrote about how you can reduce your Windows Server footprint by replacing your Windows DNS server with […]
[…] Barker shares how to set up a simple unbound DNS server on PhotonOS (as he points out, a good replacement for an expensive Windows Server […]
[…] you are trying to cut down your home lab infrastructure, this blog on running PhotonOS as DNS server and NTP server is […]
Thanks for this blog. Helped me setting up the homelab. All other DNS setup and not easy.
Remember to do the following
systemctl disable systemd-resolved
[…] Here is an article I found helpful: in getting me started: Installing a DNS Server on Photon OS […]