This is a very quick post on the use of SSL certificates and vSphere.
As of vSphere 6.0 and beyond VMware have provided a VMCA (VMware Certificate Authority) which by default signs all vSphere SSL certificates (vCenter Server & ESXi)
The VCSA is a Platform Services Controller feature, enabled by default. This means that no matter if you use an embedded PSC or an external PSC, you have a Certificate Authority in place already that has signed all your VMware SSL certificates!
How do you leverage this feature?
So you might be thinking, great, but how does this help me?
Ask youself, this: How often do I get this error when logging into vCenter Server or ESXi?
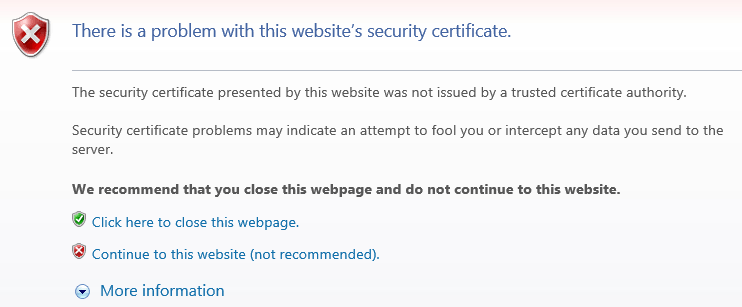
Well now that we have a CA, all we need to do is import the root CA certificates into your machines trusted root CA store and you will no longer get any certificate errors when logging into the vCenter Server or ESXi hosts. When you add new hosts, they will already be signed and trusted.
Furthermore, if the certificates are interfered with, then you will start to receive SSL errors again, at this point you will know that something suspicious is going on.
Overview
- Download trusted root CA certificates
- Import certificates into trusted root CA store
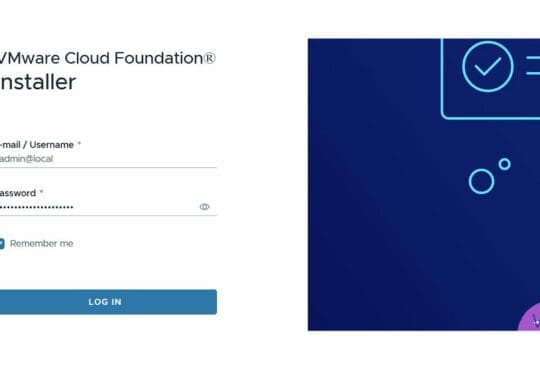
- Load vCenter Server in web browser
Detailed procedure
- In a web browser, navigate to https://Your-vCenterServer-FQDN
- On the right, select “Download trusted root CA certificates”
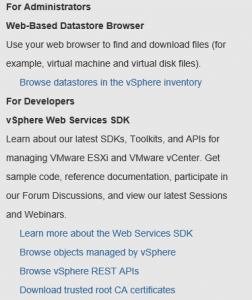
- Save the SSL certs
- Extract the downloaded .zip file
- Open the extracted folder and for Windows open the win folder
- There will be 4 files, you will want to open each of the Security certificates (Right click each and select Install Certificate)
- I want to import the trusted CA certificates into my Local Machine, so I select this option
- Select “Place all certificates in the following store”
- Hit browse
- Select the Trusted Root Certification Authorities
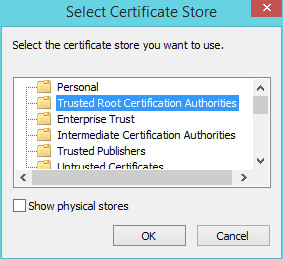
- Next, Finish, OK
Open your web browser to https://Your-vCenterServer-FQDN again and you will no longer see the certificate error
Okay not quite 1,2,3 but you get the idea! 😉