Contents
Cybersecurity is an ever-growing concern for organisations. It’s becoming more challenging to manage threats and protect your business from the increasing number of vulnerabilities.
Choosing the right tool to help identify and protect your business from such threats is also challenging. Fortunately, there are impressive products and services available to assist with these challenges. When searching for a solution, it’s always important to find a tool that gives you maximum ROI. Such tools are the ones which deal with all areas, in this cybersecurity orientated world this would include continuous identification, analysis and protection. Fortunately a US based company, IntSights exists with an ideal solution which meet these criteria.
Introducing IntSights
IntSights was formed in 2015 and set out to change the way companies protect themselves from the ever-increasing number of cyber threats. The solutions they built enable companies to detect, review and prevent cyber threats from across the web.
The IntSights product suite contains a number of solutions that helps move organisations from a reactive nature to a proactive way of preventing threats from affecting their businesses.
Threat Command
First and foremost it’s important to discuss Threat Command. Threat Command offers all the typical external threat monitoring capabilities. In addition to these, it allows businesses to act fast. Threats are detected quickly and are organised in such a way that you can take action with a single click.
Single click remediation required integration with your on-prem solutions. It is this powerful integration function of Threat Command which allows for incredible fast remediation for detected threats.
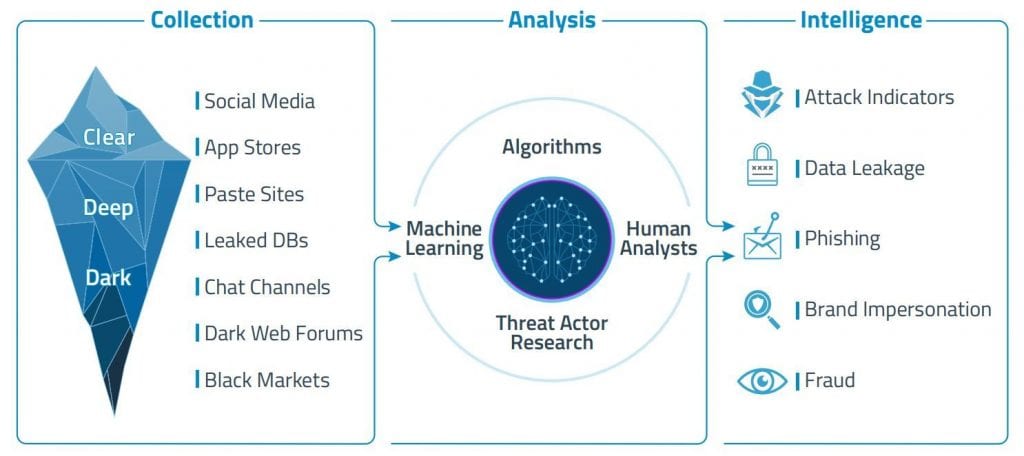
With machine-learning algorithms, Threat Command can filter and effortlessly delivery alerts to your teams, improving response times and reducing the chances of a successful attack on your systems.
Threat Command doesn’t just protect your business against system attacks. The capabilities of the solution also collect, analyse and provide intelligence on other threat types including Data Leaks, Phishing and Brand Impersonation.
The diagram below best illustrates the capabilities of Threat Command:
Further information about IntSights Threat Command can be found here: https://intsights.com/products/threat-command
Threat Intelligence Platform (TIP)
Key for DevSecOps
IntSights TIP builds on the Threat Command solution, offering customizable output and relevant threat intelligence. No longer does your team need to manually manage threats or read through thousands of alerts.
The TIP solution is key for DevSecOps, enabling you to to manage threats effectively and act fast.
An all in one platform
TIP can be thought of as an all in one external threat management and protection platform. The IntSights TIP solution provides a single pane of glass for managing threat data from various sources.
Having a single pane of glass has significant benefits, bringing in data from all sources into a single user interface reduces management overhead and frees up valuable time which can be spent proactively managing your systems.
The TIP platform boasts impressive integration with security platforms, enabling a strong, dynamic threat prevention strategy against threats from the outside world.
Actionable Intelligence
Real-time threat analysis, ranking and remediation are central to the Threat Intelligence Platform. Instead of simply providing threat data for review, TIP also provides actionable intelligence.
Insights into the data behind the threat are made available for analysis. This makes it easy to better understand a threat and to act proactively, proportionately and accordingly.
More information on how this works can be found in the Investigation API whitepaper.
To evaluate solutions from IntSights further, including their cloud offerings be sure to request a free Threat Intelligence Report https://intsights.com/free-report/request or request a demo https://intsights.com/request-a-demo
Disclaimer: Although this is a sponsored post, all opinions are my own and IntSights did not have any influence on the content of this post.